|
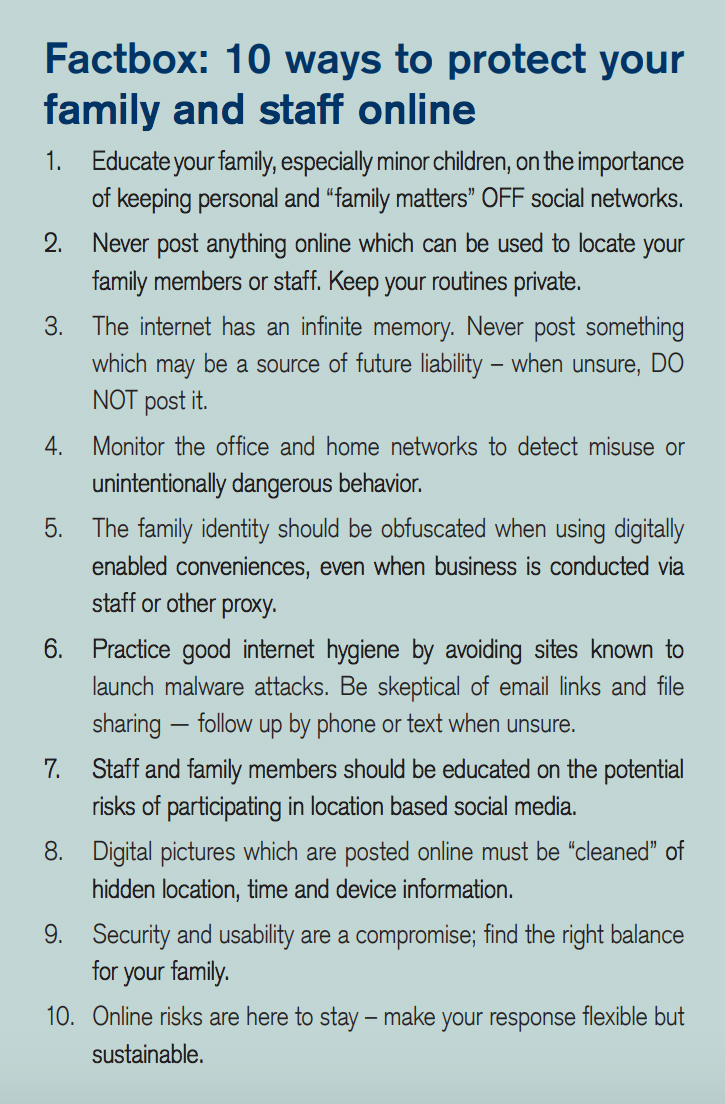
By Bailey McCann Family offices have a higher profile than ever before. The rise of social media, along with the expectation that businesses have an online presence means families have to navigate a growing risk landscape. Security studies routinely show that cybercriminals, identity thieves and burglars follow families, family members and employees online to try and get access to assets or information. An increasing connection between online stalking and physical violence adds yet another potential layer of danger for individuals. As a result, families are rethinking how they manage what is posted online and crafting policies designed to protect individuals and employees. Prevention, Policies & Monitoring Those of us who work with families have really shifted how we talk and think about online risk, says Patricia Soldano, a family office consultant based in California. Michelle Jordan who has done work in this area calls it reputation responsibility - and it really involves being proactive about risk prevention, but also putting a policy in place that outlines how information is shared as well as response plans in the event of an incident. Thinking of your online presence as a responsibility instead of just another issue to be managed can help family members young and old alike take their inter- actions a little more seriously. Making it a responsibility to administer devices like cell phones and computers such that they are always running current software and have current security patches also limits potential vulnerability. Jordan Arnold, who heads K2 Intelligences Private Client Ser- vices, Strategic Risk and Security practices, works with families on creating these policies as well as managing devices and incident response. K2 Intelligence was founded by the Kroll family, the originators of modern corporate investigations. Arnold says families have finally started to understand that prevention is much easier than dealing with the potentially permanent harm of an irresponsible post on social media or opening an attachment without checking if its real. The issue is when it comes to online incidents, the damage is permanent. It is very hard to remove information once its out there. You can delete a post but someone could have taken a screenshot. Or, if you have poor online security, its like leaving the door open, he says. Avoid real-time posts Arnold adds that the best way to understand the risk is to think of your digital life as a footprint. We advise families, for example, to post on a delay. If you post real-time from where you are you are creating effectively two risks. Youve created a physical risk wherever youve posted from and an asset risk at your home or business because adversaries now understand you arent there. Even when individuals post on a delay, they shouldnt include overly specific locations or identifying details. That could mean anything from hotel rooms to the interior of offices. Its one thing if an online lurker knows youre in Paris, its another thing if they know at which hotel. Similarly, online adversaries that are looking for business information may be able to take away key bits of intelligence from whats in an image of an office, conference room or other work areas. You might think a picture looks totally innocuous but you have to think about all the information that is in that image, Arnold says. As part of its risk management practice for families, K2 Intelligence monitors databases of stolen information for details about their clients. A whopping 40-60 percent of those families have had information on one or more of those databases. You dont necessarily have to hack someone to get personal information anymore, he notes. Its often about what individuals freely give up without thinking about it. This is where changing mindsets around what goes online is a key part of prevention. Basic cybersecurity training, crafting online policies and implementing solid monitoring tools also help. Focus on the whole organization Timothy Lappen, founder and chairman of the family office and luxury homes groups at Jeffer Mangels Butler & Mitchell LLP, says its important to be realis- tic about what people are willing to do in the name of security. You can implement all the best systems in the world, but if they arent easy to use they are going to fail, he says. In some cases, the response is well, we just wont be online because the risks are too great. But, thats not realistic in this day and age. Lappen suggests that getting cybersecurity insurance can be a helpful safety net if situations arise. Cybersecurity policies can insure devices, business activities and other online transactions provided that the family completes a risk audit with the insurer. If a compromise occurs the insurance policy can help recover lost or stolen data as well as covering the cost of security response. However, coverage can be denied if insurers find that organizations werent staying on top of best practices for information sharing and cybersecurity. Most enterprises monitor activity internally in an effort to prevent activities that might trigger an insurance claim or security response. This practice is growing in family offices as well. Monitoring what people are doing online within the organization can be fraught - especially for families - but it can also prevent violence and insider threats. Security consulting firm Hillard Heintze works with companies and families to monitor how family members and employees are interacting online. In one case study, an employee set off an internal security trigger by posting about another employee on Facebook. The post suggested the potential for violence. Hillard Heintze worked with the organization as well as law enforcement to indentify the people involved and craft a response plan. Parties were able to come together and prevent violence by temporarily reassigning the employee under threat and ending employment with the person who made the threat. Without strong monitoring, the situation may have unfolded differently. Kids can be but arent necessarily the weak link Many parents also strictly limit screen time for their children or refuse to let them have their own devices. That can work at a young age, but it gets harder as kids age and more of daily life and indeed school- work must be completed online. Complex security procedures can also be hard for adults to stick to if they are in a hurry or think they know better. Patricia Saldano notes that its not always the kids that are the weak link when it comes to being online. I work with a lot of young people and Im seeing more of them that arent online or on social media that much or they were on it and ended up leaving it. They tend to be more aware of the potential risks compared to older people, who see it as a way of staying in touch, she explains. Anecdotally, I see more older people on social media and they seem to have varying degrees of understanding about what it all means. By working with a risk team that includes cyber- security professionals, lawyers, insurers and crisis communications firms families can create a barrier of protection from online adversaries. Prevention is critical, once something is online or information is compromised it becomes very difficult to remove it. All members of the family and employees should know what the policies are and also have a working understanding of the risks of social media and other online transactions. Creating a device program can also help ensure that up-to-date software is present throughout the organization. Finally, a strong monitoring process can help ensure a rapid response if a compromise does occur.
| ||||
|
Horizons: Family Office & Investor Magazine
Managing Online Risks to Family Offices |
|





 RSS
RSS